This article is about Cyber Security
Ways to avoid Phishing Scams
By NIIT Editorial
Published on 06/02/2022
6 minutes
Phishing attacks are not new to mankind. They have been around since the dawn of the internet age and have only evolved in their style of functioning. Described briefly, phishing is a type of attack wherein the hacker broadcasts a masqueraded message to coerce the reader/user to share confidential information. Another form of phishing is when ransomware is installed on the users’ devices for exploitation. Believe it or not but phishing is a type of scam that you can prevent yourself from falling into. Here are the 10 to-dos you must abide by if you are to circumscribe phishing unscathed.
Stay up to date with the latest on Phishing Attacks
When you stop reading, you stop growing. Therefore, even if cybersecurity isn’t one of your interests, you should at least know enough about the many ways hackers have employed, in order to stay safe. Learners can even enroll in cybersecurity certifications online to study the same.
Click at your own risk
Netizens are inundated by the volume of ads that brands run to target them. On trusted websites, it is within the accepted norms to click randomly on an ad that appears on-screen. However, the same doesn’t hold true for unsecured websites. Phishing links redirect people to websites that may look legitimate. But on closer inspection, it is not hard to make out the difference. The sign-up forms that you are often presented on landing pages could hold that card to its credibility. Since hackers broadcast ads randomly, they may not have critical data such as your name. Due to this, the targeted collateral for phishing might begin from “Dear customer” rather than the address you personally.
Verify Site Security
The best way to identify a site’s security is to look for the symbol of a lock in the upper right-hand corner of the browser. If the icon is closed then it is a confirmation of the same. In addition to it, the website URL should begin with an “HTTPS” and not “HTTP”. The third point that you should consider before sharing information with a website is the message prompt displayed by your browser. In cases when the browser cannot authenticate the website servers, it displays a message saying the “site might contain malicious software”. Steer clear from such dubious pages. Often search engines can display landing pages that may boast an array of cheaper/discounted products. Often, such front ends are a disguise to capture the financial credentials of customers, to be exploited later. Many cybersecurity certifications online have begun disseminating methods to recognize such anomalies in websites.
Change Your Passwords Regularly
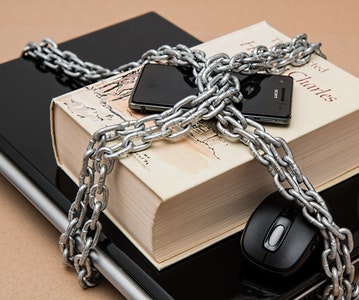
It is a good habit to change your password every now and then. Dormant online accounts are an attraction for hackers who can employ digital espionage to commit data theft. It is recommended that you reconcile bank statements against monthly expenditures and stay vigilant.
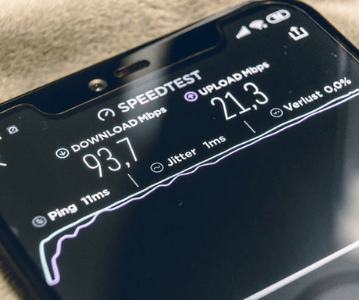
Update Your Browser
Security patches are the software improvements that should be installed to cover for hitherto loopholes. Following routine debugging audits, when your browser suggests a new update is available, you should install it right away.
Employ Firewalls
Nowadays, many cyber security certifications include modules on firewalls for learners, and for good reason. It is because firewalls act as a barrier to entry for non-verifiable sources of data. It is of two types. The first is a desktop firewall and the second is a network firewall. Coupled together, they prevent otherwise undetectable attempts to harm your system.
Ignore Pop-ups
Malware often poses a threat in the form of innocuous-looking Popups. Not all popups are to be clicked. You must have come across some that (although) did contain a “cancel” button but did not close even when you clicked the same. Instead, what you should do to get rid of the same is to click the (x) button that appears on the upper right-hand corner of the box.
Use Antivirus
Even the best cyber security courses online cannot downplay the importance of having an antivirus. Antiviruses are used to identify, detect, and delete harmful malware/viruses that otherwise remain obscure to human observation. Symantec is the supposed leader of the antivirus marketplace. Similar anti-malware software vendors include Avast, McAfee, and ESET.
If online search trends are to be believed, then millennials are very much interested in pursuing a cyber security course online. While some want to begin right at the foundational level, others want to upskill in advanced concepts. NIIT offers an alternative for both cohorts. The Foundation Program in IT Infrastructure and Security is a first-level course for anyone interested in establishing an understanding of cybersecurity. Similarly, the Cybersecurity Program is a placement-assured course that enables program-enrolees to become day-1 job-ready in cyber competencies. Explore the certifications now for a satisfying career trajectory.
Cybersecurity Program
Be job-ready! Earn a min. CTC of ₹4LPA with this placement-assured program*
Placement Assured Program*
Flexible Payment Option