This article is about Cyber Security
Essential Skills Required by Cyber Security Professionals
By NIIT Editorial
Published on 18/09/2021
6 minutes
Cybersecurity is throbbing with investor activity. In the time elapsed since 2017 and ending with 2021, global cybersecurity spending is projected to cross the $1 trillion dollar mark. But there is another estimate that needs to be mentioned that runs in correspondence with the growth of the industry. It is estimated that global financial losses due to cybercrime will amount to $10.5 trillion by the year 2025.
Considering the dire circumstances which are poised to get worse, there is a widening void for cyber professionals to come forwards and contribute with essential cyber expertise. With that in mind, we share with you the top 5 skills to target if you want to be part of the cybersecurity industry.
Malware Analysis
Malware is an abbreviated version of the words malicious software. The purpose of malware is to grant illegitimate access to unauthorized networks for stealing/leaking critical business information. There are 11 types of malware that businesses need protection from such as:
- Ransomware
- Fileless Malware
- Spyware
- Adware
- Trojans
- Worms
- Rootkits
- Keyloggers
- Bots
- Mobile Malware
Before you know it, the software can give shape to thefts and cause unimaginable damage to the business. Professionals with the requisite acumen to identify and activate damage limitation against malware are highly sought after.
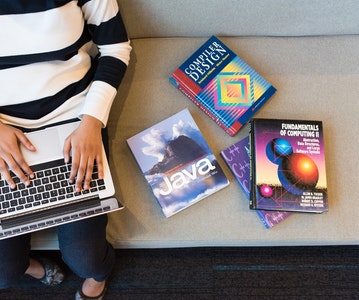
Programing
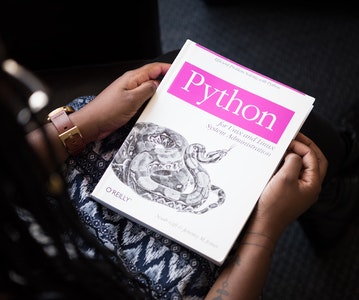
Knowing multiple programming languages is always welcome, especially those that run the show for cyberinfrastructure. Beginning with low-level languages such as C and C++ cyber analysts are expected to code in Python, a programming language that allows application integration, and is a key enabler for statistical analysis. AI, ML models can be created using the same to strengthen the grip on security. Python is also used to run website navigating scripts, perform malware analysis, as well as develop in-house security breach controls without the dependence on third-party software. PHP and SQL are a couple of other programming languages that you are expected to know.
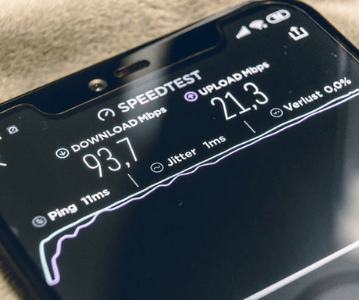
Networking
Networking is a standalone IT field in itself but can easily be aligned with the needs of cybersecurity. Professionals that are already well-versed with networking can focus on the following specialization areas within cybersecurity:
- Information Security
- Cryptography
- Risk Assessment and Management
- Miscellaneous Security Operations
Having an experience with Linux and project management would help in landing interviews in the field.
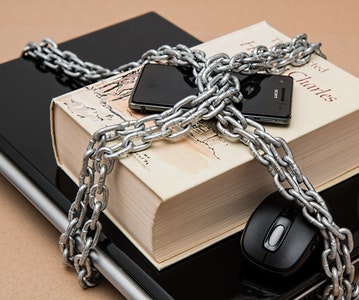
Encryption & Cryptography
Hackers target communication channels that are often not encoded from end-to-end. Data encryption can save such a data leak and make transfer channels fail-proof. Also, malevolent actors could try and target non-certified applications installed on company premises that might be opening the door to a hack.
To tackle such threats cryptographers are needed that with subject matter expertise in core mathematical algorithms, linear algebra, combinatorics, and the number theory. In addition to this, encryption techniques such as the symmetric encryption method, asymmetric encryption method, and hashing have found useful applications in the cyber world.
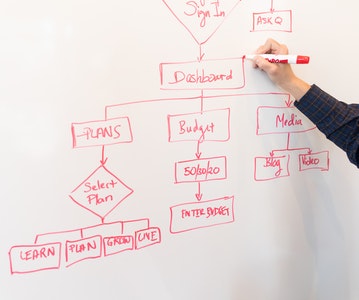
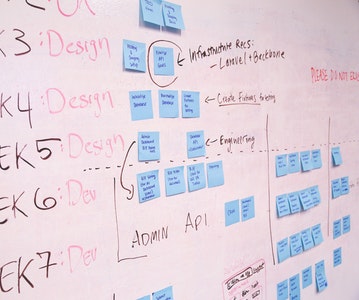
Threat Modelling
Threat modeling refers to the advance preparation in anticipation and aversion of cyber threats. Techniques such as STRIDE (Spoofing, Tampering, Repudiation, Information Disclosure, Denial-of-Service, Elevation of Privilege), DREAD (Damage Potential, Reproducibility, Exploitability, Affected Users, Discoverability), and VAST (Visual, Agile, Simple Threat modeling) are commonly used to position online defenses and prevent data breaches. From the business process to networks, and applications threat modeling offers a route to systematically secure your infrastructure and offer secure products/services to customers.
There’s More to the Story
Its true that the aforementioned fields are required to grow in the cyber security workspace but there’s more to it than meets the eye. StackRoute’s Advanced Post Graduate Program in Cybersecurity & SecOps is a certification at par with industry standards, recruiter-demand and learner expectations. Professional growth does not require just technical expertise but also a variable x-factor component that makes you think out of the box. This program will help you align your intellect in line with real world cyber security scenarios.
Apply now!
Advanced PGP in Cybersecurity and SecOps
Become an industry-ready StackRoute Certified Cybersecurity Analyst. This program transforms learners with no Information Technology background into cybersecurity specialists. This is a Job-Assured Program with a minimum CTC of ₹ 5LPA*
Job Assurance*
Flexible Payment Option