This article is about Cyber Security
What is the Whaling Phishing Technique
By NIIT Editorial
Published on 11/02/2002
6 minutes
Whaling is a highly targeted phishing attack aimed at executives disguised as legitimate emails. Whaling is a digitally-enabled social engineering scam designed to encourage victims to take secondary actions, such as initiating the transfer of funds.
Whaling does not require extensive technical knowledge, but it can be very beneficial. So this is one of the biggest risks for businesses. While financial institutions and payment services are the most targeted organizations, cloud storage, and file hosting sites, online services, and e-commerce sites are more likely to be attacked. Whaling emails are more sophisticated than regular phishing emails. Whaling email is a form of social engineering aimed at encouraging victims to take secondary actions such as:
Data Loss
Clicking a link or downloading an email attachment can infect your corporate network with malware. This can lead to data breaches such as customer data loss and intellectual property theft.
Damage to reputation Economic or data loss as a result of whaling can be very embarrassing for both businesses and individuals.
Initially, whaling emails were less difficult to identify than nontargeted phishing emails. However, the introduction of fluent business terminology, industry knowledge, personal references, and fake email addresses makes it difficult to identify sophisticated whaling emails even with careful eyes. Targeted content is combined with several other methods that business leaders need to know to reduce their potential victims of whaling attacks.
Whaling email by phone
This is a social engineering tactic that can be described as a cyber-assisted scam. The phone serves two purposes: to confirm the email request and to satisfy the victim in the event of a potential cyberattack. This is because the victims also interacted in the "real world." The increase in whaling emails from malicious attackers disguised as trusted partners' supply chain attacks (which are compromised to gain access to a network of suppliers or partner organizations) is well documented. However, recent whaling attacks use readily available information about suppliers and partners to create whaling emails that appear to be reliable. Whenever an organization promotes a partner such as a charity, law firm, think tank, or academic institution, it should be noted that it may receive emails from malicious actors disguised as trusted partners.
The increase in whaling emails from malicious attackers disguised as trusted partners
supply chain attacks (which are compromised to gain access to a network of suppliers or partner organizations) are well documented. I am. However, recent whaling attacks use readily available information about suppliers and partners to create whaling emails that appear to be reliable. Whenever an organization advertises a partner such as a charity, law firm, think tank, or academic institution, it should be noted that it may receive email from a malicious attacker disguised as a trusted partner.
Social Media Whaling
Online social networking is becoming more and more popular as a means of establishing business contacts, recruiting employees, and hosting discussions. However, social media accounts, both professional and individual, provide an opportunity for malicious attackers to investigate and connect with executives. They provide a gold mine of information for social engineering, and victims are often less alert to attacks on more social forums. According to Proof Point, social media phishing attacks increased by 150% in 2015.
Catch Beluga Whales
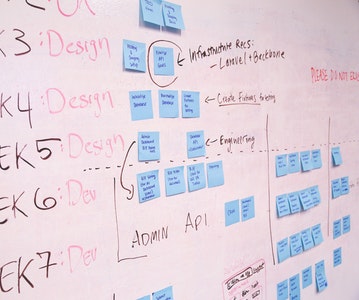
Whaling is a means of social engineering, and it is important to remember that malicious attackers use established trust structures outside the cyber realm to reassure victims. Just making employees aware of the threats posed by social engineering does not make them invincible. Some attacks are well thought out and user awareness and training cannot guarantee detection. Employee and manager training on social engineering tactics should be seen as part of a range of technical and user-based countermeasures against attacks, but be aware of the limitations of such countermeasures.
Organizations need to ensure that training is supported by enhanced technical defenses, but malicious attackers are increasingly adopting techniques to bypass automatic detection and prevent analysis of attack methods. doing. Therefore, companies need to acknowledge the potential success of whaling attacks and implement controls and processes to mitigate the damage.
Cybersecurity Program
Be job-ready! Earn a min. CTC of ₹4LPA with this placement-assured program*
Placement Assured Program*
Flexible Payment Option