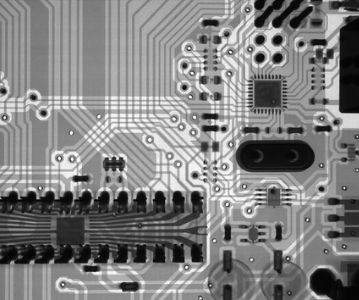
This article is about Cyber Security
Top Ethical Hacking Tools in 2021
By NIIT Editorial
Published on 04/04/2021
6 minutes
Ethical hacking is the process of penetrating the cyber workspaces of an organization with authorizations from the business owners. It is also referred to as penetration testing and performed to identify the loose ends in information security systems to rectify them before the adversaries find out. Ethical hacking is performed with tools that help gather information, decode passwords, and aid to create inlets into the digital space. Here are the top ethical hacking tools that will be used in 2021.
- Acunetix
- Nmap
- Metasploit
- Wireshark
- Nikto
- John the Ripper
- Kismet
- SQLNinja
Acunetix
This is an automated security testing tool used by ethical hackers. Its coverage includes any web application and or website that can be accessed through a browser using an HTTP/HTTPS protocol. Threats such as SQL injection, and cross-site scripting can be detected by Acunetix. The software allows you to schedule daily, weekly or monthly scans for cloud applications.
Following the audit, you can build and customize content to suit the audience. Additional features of the software include:
- Vulnerability testing
- Network scanning
- Crawl analysis
- WordPress quality check
- Risk management
Nmap
The name is an acronym for the full form Network Mapper. It is an information-gathering software that is used to accumulate data about a target. The collected information can be used to plan the strategy for an attack. Nmap is supported by all the leading operating systems such as Windows, Linux, and Mac. Additional features of this data collection cyber software include:
- Network mapping
- It offers IPvs support
- Initiating DNS queries
Metasploit
This is another penetration testing tool using which counter-methods for upgrading cybersecurity can be adopted. Network administrators can use Metasploit to find intrusion gateways into their own networks to figure out the prevalent vulnerabilities that have to be monitored, addressed, and improved upon. Even beginners can use Metasploit as the first step towards ethical hacking. Using Metasploit, you can duplicate websites and test how the website architecture reacts to phishing attacks. Additional features of the software include:
- It helps you circumvent early warning systems
- Determine the overall security conditioning
- Carry out remote attacks on assets
- Identify network hosts
John the Ripper
This one is a password cracking tool, and that too a popular one. Often, people use passwords that are also easy to crack. John the Ripper can be used to suggest adequate password strength for your device/operating system. It offers three distinct modes to operate in namely:
- Single crack mode
- Wordlist mode
- Incremental mode
Hashcat
Hashcat is a password recovery tool, and as per the company, the fastest in the world. Experts tend to favor Hashcat over John the Ripper when it comes to penetration testing for its ultra-high capabilities to crack hashes. Cryptanalysts can perform a range of password-identification attacks such as mask attacks. and the dictionary attack.
Hashcat works best on modern Graphic Processing Units than a CPU, on which you could face some laxity. Additional features of Hashcat include:
- It is free to use and open-source
- Supports multiple operating systems like Windows, Linux, & macOS
- It can crack multiple hashes at the same time
Wireshark
Cyber analysts can analyze network traffic using the open-source tool Wireshark. Wireshark is capable of detecting security problems in addition to remedying miscellaneous network problems. It is easier to present data in readable language formats making it rather simpler to come up with a proactive strategy. Additional features include:
- You can inspect multiple protocols as the Wireshark tool offers a vivid database
- Perform offline analysis
- Supports Linux, Windows, OS X, and other leading operating systems
- You can use a GUI to browse network data
Nikto
It is a vulnerability scanner that is used to analyse web servers for malicious files such as CGIs, worn-out software, and other server-related technicalities. While scanning it can capture and print the cookies for later assessment by experts. Its CGI directory has the potential to identify more than 6700 CGIs. Server configuration errors such as the presence of multiple index files and various other HTTP server options can be detected with Nikto. Other than the free version of the code that is readily available for use, iOS users will find MacNikto more suited to their needs.
Interested in Cyber Security? Explore this
The pandemic has combed out cyber inefficiencies of businesses that lacked a strong digital infrastructure. As a result of this, adversarial attempts to capture information security systems have picked up significantly. Already, an aggressive push for hiring talent in this domain can be observed. StackRoute’s Advanced Post Graduate Program in Cybersecurity & SecOps is designed to give learners the edge they need in just 18 weeks.
Explore, apply, and change your career into something you are proud of.
Advanced PGP in Cybersecurity and SecOps
Become an industry-ready StackRoute Certified Cybersecurity Analyst. This program transforms learners with no Information Technology background into cybersecurity specialists. This is a Job-Assured Program with a minimum CTC of ₹ 5LPA*
Job Assurance*
Flexible Payment Option