This article is about Cyber Security
Types of Cyber Security Attacks
By NIIT Editorial
Published on 10/03/2021
6 minutes
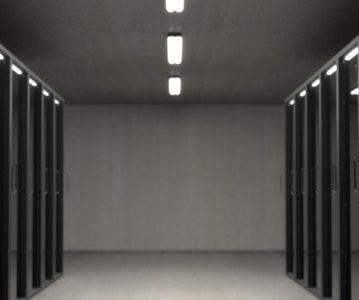
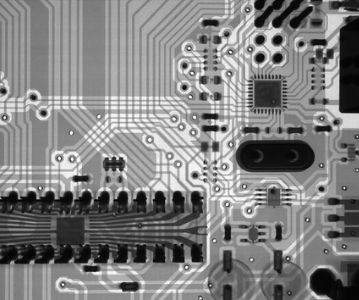
Cyber attacks can take many shapes and forms and often go undetected due to which a dedicated approach towards beefing up information security is required. Gartner predicts that this market is bound to grow up to about $170 billion by 2022. During the last year, cyber threats have grown in both frequency and intelligence. Buoyed by misinformation campaigns and financial insecurities, the public at large has been the victim of sophisticated cyber crime. It pays to think then what kind of attacks are being played upon the masses. Let us acquaint ourselves with the most recurring threats in cyber security in 2021.
Types of Cyber Attacks
Below we look at the commonly used cyber threats:
Hacking
It is embarrassing as a business to have your systems hacked into. More than a security breach, it gives users the impression that their data is not secure with you. Although an accident, mission critical secrets could be leaked into public sight that may mount legal troubles for the business owners. Cybersecurity trends 2021 project that cybercrime could cost the global economy $10.5 trillion by 2025. Having a robust infrastructure therefore becomes non-negotiable.
Phishing
Phishing involves masking harmful files as legitimate documents and sending the same to users. Phishing attacks use multimedia formats such as PDFs, java extensions, android and windows executable files, and scripts to name some. Sometimes the attacks are so well managed that users cannot make out the difference between what’s credible and what’s unauthentic. In 2020, owing to so many people working from home, the FBI reported a drastic increase in phishing attacks. As much as 241,324 phishing attacks were carried out in 2020, which is 11 times the frequency of 2016.
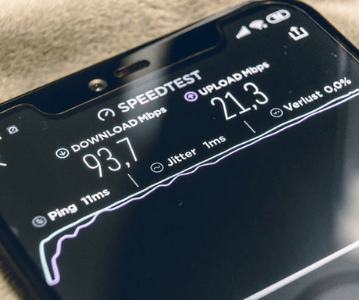
Man in the Middle Attack
Just as the name suggests, MITM happens when the hacker successfully penetrates the communication channel between 2 parties and poses as the other person. The user, not realizing what is going on, shares personal information and causes self-damage. The most frequent sources of such attacks are public WiFi networks and a variety of malware that can infiltrate computer software easily. In 2021, man-in-the-middle attacks are expected to be quite right up there alongside android malware and SMS phishing attacks in terms of damage caused.
SQL Injection
The Structured Query Language is used to process data in databases. Hackers can use the same to enter into the system and meddle with its code in order to gain critical information. An SQL injection happens mostly to websites that have a poor security layer. As per a daring statistic, SQL injection attacks represent up to 2/3rd of the attacks that are carried out on web applications.
DNS Tunneling
DNS refers to the naming system that is used to represent each device/network connected to the internet. Hackers can embed malicious code into DNs queries and responses thereby extracting sensitive information from within the system.
Malware
Malware is a shortened phrase for malicious software and can be deployed by hackers in a variety of ways to steal information from users. Ransomware, spyware, adware, trojans, and worms are all segmentations of various types of malware.
Learn how to Avert Cyber Threats
Cyber threats are evolving with the advancement of AI, ML, and IIoT. They are taking their form-factor and threat intensity levels to stealth mode. Information security systems throughout the globe need professionals with a cyber acumen capable of safeguarding enterprise data from theft. StackRoute’s Advanced Post Graduate Program in Cybersecurity & SecOps is a MOOC designed to fulfil this growing industry need.
Enrol now and stand a chance to make the most of a high-paying cyber security job.
Advanced PGP in Cybersecurity and SecOps
Become an industry-ready StackRoute Certified Cybersecurity Analyst. This program transforms learners with no Information Technology background into cybersecurity specialists. This is a Job-Assured Program with a minimum CTC of ₹ 5LPA*
Job Assurance*
Flexible Payment Option