This article is about Cyber Security
An Introductory Checklist on the Types of Malware
By NIIT Editorial
Published on 05/02/2021
5 minutes
Malware is an acronym that combines two words, malicious and software. It is used by rogue actors to unethically extract critical data, legitimise access to a network or block entry for authorized personnel into information systems. As per the International Monetary Fund, cyber-attacks cause damages over $100 billion dollars to financial institutions annually.
Malware is a major cause of that and no amount of intel will prove enough to dodge the negative impact of such attacks as technological complexities continue to widen the gap between tight and loose. With that in mind, this listicle would act as a primer for anyone who wants to know the variety of malware there are in general knowledge.
Ransomware
This type of malware blockades the access for users to their data until a ransom has been released. It uses encryption for the block and upon releasing the payment, only a decryption key can unlock it. However, the payment is no guarantee to reinstate the access as the decision is at the behest of the hacker.
Fileless Malware
They are one of the most dangerous malware to deal with due to their stealthy nature. It corrodes and changes the original files on the operating system instead of attacking it openly. They can stay
undetected for a long time despite using antivirus software.
Spyware
This malware is capable of collecting user information such as passwords, saved notes, photographs, etc. without their information. An aspect that increases its seriousness is the fact that unlike malware that is desktop specific, spyware can operate on a variety of devices such as smartphones, tablets, and laptops.
Adware
This malware is much less harmful in terms of a financial loss to the user but it violates something much more personal than money, privacy. Adware collects a users’ internet browsing history and shares it with the hacker. The data is sold to advertisers who can run interest-specific ads and offer lucrative ROIs. User consent is never sought as they are practically unaware of the undergoing procedure.
Trojans
Trojans pose as your household software but are actually a corrupt replica instead. Once duped, the user downloads the software/code on their device at which point the trojan begins to collect user information. If enough information is gathered, the trojan has the potential to lock you out of your device.
Worms
Technology cannot be infallible. Worms have the ability to identify and exploit systemic loopholes in the OS following which they get activated and begin accessing the network. Distributed Denial of Service (DDoS) attacks can be plotted by Worms.
Rootkits
This malware hands administrative control of the device to the hackers. The most common mediums through which they spread include phishing emails, malicious software downloads, and shared drives.
Keyloggers
Ironically, keyloggers are used for legitimate purposes as well. Their fundamental use is in tracking user device activity. A lot of corporations use it to optimize worker productivity. There are applications that employ the use of Keyloggers to restrict internet use by children.
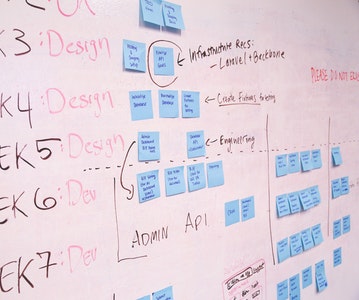
Advanced PGP in Cybersecurity and SecOps
Become an industry-ready StackRoute Certified Cybersecurity Analyst. This program transforms learners with no Information Technology background into cybersecurity specialists. This is a Job-Assured Program with a minimum CTC of ₹ 5LPA*
Job Assurance*
Flexible Payment Option