This article is about Cloud Computing
What Is The Difference Between Private Key And Public Key?
By NIIT Editorial
Published on 14/11/2021
8 minutes
Several experts recommend having a detailed look at the difference between private key and public-key cryptography. There was a time when two detectives would greet each other with a code word when they met outside on a mission in old Bollywood movies.
Here, both parties continue to communicate using the code word. The codeword protected confidential and sensitive information. In today's internet-based world, while most communication takes place online, it is imperative to protect the data and information from cyberattacks.
Cryptography
Cryptography is a two-part process cloud service that involves encryption and decryption, using cipher as the key. It is a procedure wherein a cloud provider adds a cipher to the plaintext to convert it into ciphertext, decoded by the receiver with the key, leading to secure communication. It is possible to detect interception during this process. It is good to learn about them in any DevOps online training or pursue an online cloud computing course.
Cipher suites use unique algorithms for encryption and encoding during transmission and use different algorithms for message authentication at the receiver's end. A public and private key is required to encrypt the entire process from a data center, embedded in protocols and software codes.
What Is A Private Key?
Data can be encrypted as well as decrypted using this type of key from a data center. Both the sender and the receiver of the sensitive, encrypted information share the same private key. Symmetric keys are sometimes referred to as two-sided keys.
Here, the two parties share the same critical cloud service. To put it simply, the other party shares or copies the same encryption key for decrypting the ciphertext. This mechanism is faster than public-key cryptography. With a private key, you can use the same key for encryption and decryption.
What Is A Public Key?
With this type of key, a user or a cloud provider can encrypt the data available, while the private key can decrypt it. To put it simply, a user can encrypt data using a public key. The receiver uses a private key for the decryption of the ciphertext. Symmetric cryptography is also known as the public key.
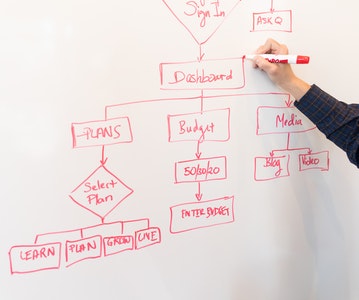
DIFFERENCE BETWEEN PUBLIC AND PRIVATE KEYS
One can acquire more in-depth knowledge about these differences also from the best Online DevOps or Cloud training program.
- Speed
It is much faster to generate a private key than a public key.
- Authenticity
A symmetric-key cryptographic private key is used to encrypt the message during a conversation using the same key. In contrast, in asymmetric key cryptography, there are two keys, one that is used during encryption and the other one that is used during decryption at the receiver's end.
- Secret
The sender and receiver are the only people who know the private key with a private key. A public key is visible to everyone and can be viewed by everyone, including a cloud provider recipient.
- Aim
System speed, reliability, and security are tested through private key cryptography or cloud service. The essential public testing is more long-term in nature and assesses the sustainability of the system. Using the same key for transmission and receiving is called symmetric-key cryptography, and using different keys is called asymmetric key cryptography. In simpler terms, the significant difference between symmetric and asymmetric cryptography is in the key used by the sender and the receiver.
WhatsApp, which promises end-to-end encryption, is one of the most recognizable examples of public-key cryptography. Asymmetric key cryptography uses public-key cryptography, so only the intended individual has the private key.
When WhatsApp is installed on a device, the server registers public keys, and the messages are communicated securely using private keys. Asymmetric key cryptography uses public-key cryptography, so only the intended individual has the private key.
End-to-end secure payments are becoming increasingly important using UPI, digital wallets, and internet banking. Banks and Payment Gateways use cryptographs to prevent the risk of Malware and Hackers.
In A Nutshell
Over time, cryptography has developed and has become more secure against potential attacks, cyber crimes, threats, etc. You can understand from studying symmetric and asymmetric types of cryptography that digital transactions are secured because they are encoded using mathematical algorithms.
These Algorithms function as a lock-and-key system from a DevOps online training program; Quantum cryptography is now being used to make this process even more secure than before. There is a series of photons transmission from the sender, which is then polarized by a polarizing beam or polarizing filter, resulting in a data chain.
Received sequences are decoded and returned to the sender by the receiver. A photon is only considered for transmission if it is not intercepted, and the others are discarded. As a result, confidential information is kept secure. The security of transactions becomes more critical with digitization and e-commerce, along with a data center. You can prevent cyber frauds and interceptions using cryptography.
Cloud Computing and SysOps Program
Become an industry-ready StackRoute Certified Cloud IT Administrator and get skilled to acquire all the critical competencies required to take on the role of a Cloud IT Administrator including building strong foundations as Systems administrator. This is a Placement Assured Program* with a minimum CTC of ₹ 4LPA*
Placement Assured Program*
12 Weeks Program