This article is about Cyber Security
Stay mindful of these cracks in a cryptographic system
By NIIT Editorial
Published on 05/01/2022
6 minutes
Cryptography is the study and use of approaches for secure communication when outsiders, known as adversaries, are present. Cryptography is concerned with establishing and dismantling rules that prevent outsiders or the general public from reading private messages. Different aspects of data security, including validation, information categorization, and non-repudiation, are crucial in the modern cyber ecosystem. Modern cryptography occurs at the intersection of arithmetic, software engineering, electrical engineering, correspondence science, and material science.
Electronic trade, chip-based payment cards, computerized monetary standards, PC passwords, and military correspondences are all examples of cryptography in use. Cryptography is entirely safe, according to popular belief among internet users. That is not the case, though. Vulnerabilities, one of the most commonly utilized approaches for safeguarding communications, come with various hazards. Examine the number of data breaches that cryptographic systems are vulnerable to.
Key Lifetimes
Both symmetric and open key cryptography computations are only as good as the length of the keys. The longer a mysterious or private key is used, the more vulnerable it becomes to attack. The greater the amount of data encoded with a key over time, the longer it is used. An attacker with a longer key has more opportunities to exploit flaws in the cryptography computation or execution. Overall, the more critical the data that a key will protect, the shorter the key lives must be. The shorter lifetime restricts the amount of ciphertext available for cryptanalysis and minimizes the data breach that one can do if a key sells after a successful key attack.
Length Of The Public Key
Open key cryptography is more susceptible to attacks than symmetric key encryption when given a key of the same length, especially in calculating assaults. In a contemplating attack, the attacker attempts to unscramble ciphertext using the possible combinations of integers that one may use with the computation. Considerations are similar to key pursuit assaults, but the number of possible factors varies with each computation. When everything is said and done, a figuring attack on an open key takes fewer attempts to be successful than a key pursuit assault on a symmetric key for a given key length. You can learn to protect your data with the help of cyber security certifications.
Symmetric Key Length
Key inquiry attacks, also known as animal power attacks, are a threat to symmetric key encryption. The attacker attempts every possible key in these attacks until they discover the proper key to decode the message. Most attacks are successful before they try all possible keys. By choosing shorter key lives and longer key lengths, you may reduce the risk of key inquiry attacks. A shorter key lifespan means that each key scrambles less data, reducing the risk of a data compromise if one of the keys is lost.
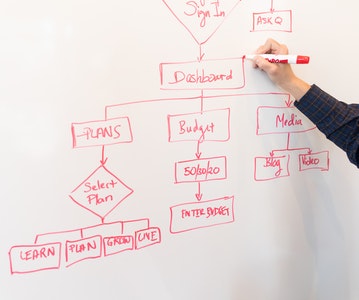
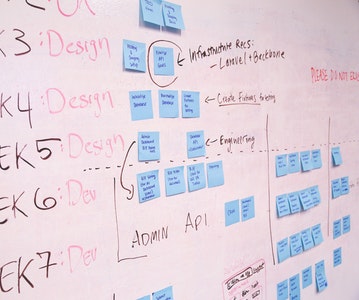
Protocols' Effectiveness
Security breakthroughs based on cryptography occur using security conventions. The S/MIME convention, for example, may be used to provide secure mail frameworks, while one can use the IPSec suite of conventions to implement secure system interchanges. In the same way, the TLS protocol can provide secure Web exchanges. Even the best application of convention standards is subject to the inherent flaws and restrictions of the measurements. Furthermore, convention standards usually allow the plan to provide support for weaker cryptography. Hence, study cyber security to ensure safe cryptographic practices.
Generated Keys' Randomness
Keys must be created arbitrarily to avoid key age from being unexpected. In the best-case scenario, programming key generators employ pseudo-irregular techniques to ensure that no one can predict which keys will occur. However, if an attacker can predict the major parameters used as part of the key age, they may also predict what keys will occur.
When properly implemented, programming-based key age provides acceptable security for a wide range of system and data security requirements. Regardless of how effectively one implements the irregular key generator, there is always a slight danger associated with programming produced keys. Consider delivering security solutions that provide random, equipment-generated keys in this manner to provide the highest level of assurance for sensitive data.
Conclusion
Cryptography is a beautiful tool, but people misuse it in a variety of ways. Attempting to develop a bespoke implementation of anything leads to several cryptographic failures and various types of cyberattacks. Most acceptable uses of cryptography have at least one library that appropriately and securely implements the feature. As a result, keep to average liabilities. Cyber security courses online can teach you ways to protect data integrity.
Cybersecurity Program
Be job-ready! Earn a min. CTC of ₹4LPA with this placement-assured program*
Placement Assured Program*
Flexible Payment Option