This article is about Cloud Computing
Implementation of Cloud using Python and Introduction to Python Forensics
By NIIT Editorial
Published on 20/08/2021
8 minutes
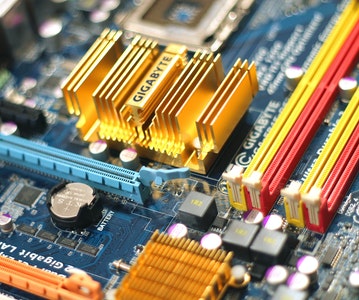
Cloud computing, in simple terms, is a set of hosted services that are made available to consumers via the Internet. It allows companies to compute or consume resources, such as Virtual Machines (VMs), applications as a service, or storage.
One of the most significant benefits of developing applications in the Python programming language is the flexibility to deploy apps practically on any platform, including cloud computing platforms. Thus, Python can run on cloud servers and portable devices such as desktop computers, tablets, and smartphones.
One of the most intriguing views is the creation of a cloud base via Rainbow tables. This makes it possible to integrate the application's single-processing and multiprocessing versions, but this needs few considerations.
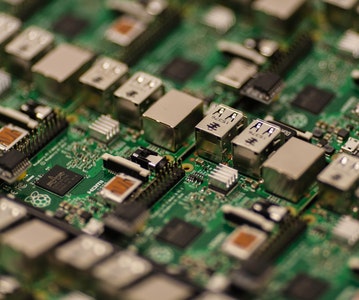
Pi Cloud
Pi Cloud is a platform for cloud computing that combines the Python programming language with the processing power of AWS (Amazon Web Services) to provide a seamless user experience.
Look at a simple example of how to build Pi clouds using rainbow tables in Python.
Rainbow Tables
When it comes to hash algorithms, a rainbow table is described as a set of all probable plain text permutations of encrypted passwords unique to that hash method.
- Rainbow tables are created using patterns that are standard, resulting in a list of hashed passwords being generated.
- An encrypted text file is used to create passwords that contain characters or plain text of passwords to be encrypted. These are then saved in a text file.
- The file is utilized by Pi cloud, which is stored in the main function.
- The output of hashed passwords is also saved in a text file with the passwords.
This algorithm can be used to save passwords in the database and have backup storage in the cloud system.
In the following in-built program, one can create a list of encrypted passwords and save them in a text file.
Example
import os
import random
import hashlib
import string
import enchant
import cloud
def randomword(length):
return ''.join(random.choice(string.lowercase) for i in range(length))
print('Author- Radhika Subramanian')
def mainroutine():
engdict = enchant.Dict("en_US")
fileb = open("password.txt","a+")
# capture the values from password.txt file.
while True:
randomword0 = randomword(6)
if engdict.check(randomword0) == True:
randomKey0 = randomword0+str(random.randint(0,99))
elif engdict.check(randomword0) == False:
englist = engdict.suggest(randomword0)
if len(englist) > 0:
randomKey0 = englist[0]+str(random.randint(0,99))
else:
randomKey0 = randomword0+str(random.randint(0,99))
randomword3 = randomword(5)
if engdict.check(randomword3) == True:
randomKey3 = randomword3+str(random.randint(0,99))
elif engdict.check(randomword3) == False:
englist = engdict.suggest(randomword3)
if len(englist) > 0:
randomKey3 = englist[0]+str(random.randint(0,99))
else:
randomKey3 = randomword3+str(random.randint(0,99))
if 'randomKey0' and 'randomKey3' and 'randomKey1' in locals():
whasher0 = hashlib.new("md5")
whasher0.update(randomKey0)
whasher3 = hashlib.new("md5")
whasher3.update(randomKey3)
whasher1 = hashlib.new("md5")
whasher1.update(randomKey1)
print(randomKey0+" + "+str(whasher0.hexdigest())+"\n")
print(randomKey3+" + "+str(whasher3.hexdigest())+"\n")
print(randomKey1+" + "+str(whasher1.hexdigest())+"\n")
fileb.write(randomKey0+" + "+str(whasher0.hexdigest())+"\n")
fileb.write(randomKey3+" + "+str(whasher3.hexdigest())+"\n")
fileb.write(randomKey1+" + "+str(whasher1.hexdigest())+"\n")
jid = cloud.call(randomword) #square(3) evaluated on PiCloud
cloud.result(jid)
print('Value added to cloud')
print('Password added')
mainroutine()
Output
The above given code generates this output-
These passwords are saved in the text files. The below image shows how they are visible
Python Forensics
Python is a programming language designed for ease of use by both advanced programmers and total beginners. The Python library collection consists of many helpful tools that may be utilized with any stack platform. While many labs depend on Python to create simple models for predictions and conduct experiments, Python is not used to build complex models or run extensive tests. Another advantage is that it assists in the management of prominent operational systems.
In addition to Python's built-in features, it is also designed to help investigations with digital evidence and preserve the integrity of evidence. Let's go over some of the core principles of using Python in digital or computer forensics.
What is computational forensics?
Computational forensics is a newly discovered study discipline. It describes utilizing digital techniques to solve forensic issues. The program incorporates computational science with its research on digital evidence.
The class covers a wide range of subjects involving tools, substances, and processes. Those being investigated focus mainly on pattern evidence such as tool marks, fingerprints, shoeprints, documents, and DNA, but also on physiological and behavioral patterns. Also, in the context of crime scenes, we have digital evidence such as cell phone records, IP addresses, e-mails, and social media pages.
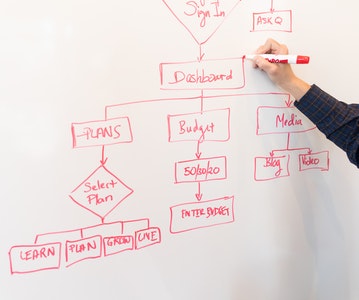
This diagram illustrates the many areas in which Computational Forensics (CF) extends.
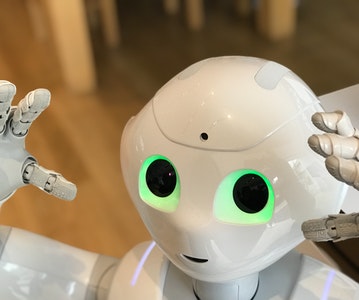
Forensic computation is accomplished using a combination of algorithms. This technology is used for processing signals and images, computer vision, and rendering graphics. Data mining, machine learning, and robots are also part of it.
In computational forensics, you will need to use many different digital techniques. To implement digital techniques for forensics in a variety of manners, a general-purpose programming language such as Python should be used.
Python Forensics - Installation of Python
Because Python is required for all of the actions associated with computational forensics, let's take it step by step and learn how to install it.
Step 1: Navigate to https://www.python.org/downloads/ and download the Python installation files that correspond to the Operating System that is currently installed on your computer.
Step 2: The installation process is simple: After downloading the installer, double-click on the exe file to begin the installation.
You will be provided with the following screen once the installation is complete.
Step 3: The third step is to configure the Python environment variables on your machine.
Step 4: Variables Once the environment variables have been configured, run the command "python" on the command line to see if the installation was successful or unsuccessful.
You should see the following on your console if your installation was successful.
Conclusion
In this article you learnt implementation of clouding using the Python language and also got familiar with the Python forensics. However, Python has vast applications. To learn those you can opt for a course that gives you insight into the language, such as the Advanced PGP in Data Science and Machine Learning.
Advanced PGP in Data Science and Machine Learning (Full Time)
Become an industry-ready StackRoute Certified Data Science professional through immersive learning of Data Analysis and Visualization, ML models, Forecasting & Predicting Models, NLP, Deep Learning and more with this Job-Assured Program with a minimum CTC of ₹5LPA*.
Job Assured Program*
Practitioner Designed