This article is about Cyber Security
An Introduction to Network Security
By NIIT Editorial
Published on 07/09/2021
6 minutes
Network security is an interdisciplinary domain. It is used to set protocols that protect the credibility, preserve authenticity, and maintain confidentiality for computer networks by virtue of hardware and software. Given the growing concerns that organizations face from adversarial actors, network security has become an essential component of enterprise security buckets.
Information security systems face cyber threats of a wide variety from the devices that connect with it, the data that goes through it, the locations, users etc. Network management tools help in monitoring, and identifying such susceptibilities alongside highlighting regulatory mishaps. Such online defence mechanisms are central to the protection and preservation of user data and business continuity. This article will touch upon ground-level aspects of network security. We will also talk about why such skills are best acquired at cloud computing training online.
How does network security work?
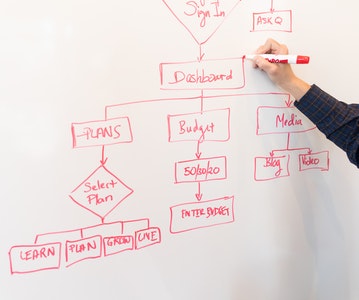
Network security comprises multiple layers. A cyber attack on any of its components could compromise operations. Which is why it is also one of the most coveted technical skills required for cloud computing. There are 3 divisions of network security:
- Physical Network Security
- Technical Network Security
- Administrative Network Security
Physical Network Security
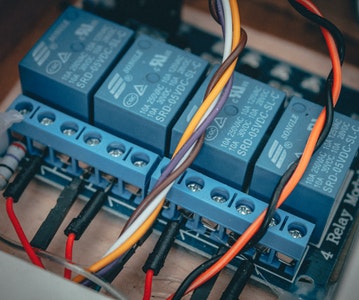
This is a layer of physical controls which are installed to block or prevent unauthorized access to business assets such as network routers, ethernet cables, lockers etc. Control systems, scanning devices such as biometrics, locks, and RFIDs are installed to enable industry-standard.
Technical Network Security
These are a set of checks and balances used to ensure digital safeguards for data stored on the network, or which is travelling through it. It provides control systems that protect both in-house employees from receiving/opening dubious files and blocking attempts from this very cohort to carry out cyber attacks.
Administrative Network Security
Speaking of user behavior, this branch of network security is used to authenticate employees. It also goes on to define the level of access each employee possesses with respect to the IT infrastructure.
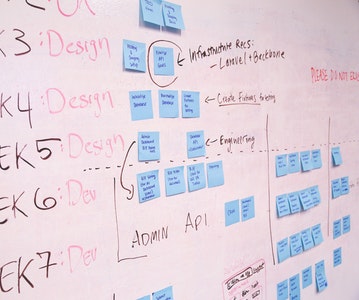
Types of Network Security Protections
Infrastructure services in cloud computing use multiple permutations and combinations of best practices and tools for safeguards. The following tools are mostly installed to ensure network security protection across the organization:
Firewall - These are responsible for maintaining control of the incoming and outgoing traffic. Anything that appears to be of a doubtful nature such as the email source, or file attachments are instantly blocked or intimated to the user for action. Firewalls have the capability to block malware attacks on network layers.
Network Segmentation - This is used to mark the boundaries of similar assets confined within a segment of the organization that perform the same function as each other. Take the perimeter gateway for instance, it separates the organizational network from the outside internet layer. This is a proven way to block harmful files from entering the system.
Access Control - These toolsets are used to block entries of unauthorized personnel and define the list of entrants who can use software/hardware assets. Identity Access Management (IAM) and Role Based Access Control (RBAC) policies make sure the people using requisite assets are sanctioned to.
Remote Access VPN - Virtual Private Networks are used to provide a safe online pathway to the company’s network. They have gained significant popularity among work from home professionals. Users install the VPN client software onto their systems. VPNs employ a series of user recognition measures such as multi-factor authentication, endpoint compliance scanning, as well as end-to-end encryption.
Zero Trust Network Access - Whereas VPNs allot access to the complete network, this approach operates with a little bit of contrast. Zero trust models state that users should be strictly granted permissions to use organizational assets that they need for professional responsibilities.
Email Security - As the name suggests, it refers to such processes and services that are used to secure email communication from getting into wrong hands. Although email service providers do offer a certain level of threat protection, that is applicable to only low-level cyber attacks. For more security against serious attacks, network security teams have to implement stringent provisions.
Data Loss Prevention (DLP) - It is in the best interest of organizations to have a DLP policy in place. It ensures that critical data such as employee credentials, and official data falling under the purview of regulatory standards such as HIPAA, GDPR, DSS, and SOX are not lost to private/unauthorized individuals.
Intrusion Prevention Systems (IPS) - IPS tools are capable of identifying and blocking threats such as brute force attacks, DDoS attacks, etc. The window of opportunity exists for hackers when they identify a network weakness and the security patch has not been applied. IPS tools are useful in intervening and preventing hackers from launching attacks.
Sandboxing - This technique is used to execute code or open files in an external environment on a device that imitates the operating system of the desired user. The purpose of doing so is to check for any anomalous behavior and use the revelation to block items deemed unsafe such as PDFs, Excel files, PowerPoint etc.
Hyperscale Network Security - It is used to scale operations by optimizing hardware/software resources to meet the rise and fall in demand for network security.
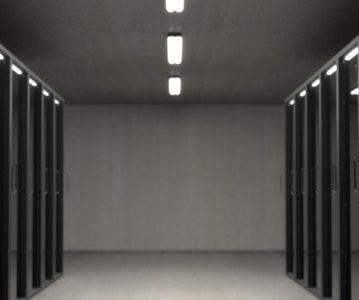
Cloud Network Security - We are in the era of cloud computing. Huge data warehouses are being used at outstation data silos to off-load storage space and save costs. Software-defined Networking (SDN) and Software-defined Wide Area Network (SD-WAN) render network services to be secure against commonly used cyber attacks.
Interested In Learning Network Security?
Learn cloud computing online with NIIT’s Foundation Program in IT Infrastructure and Security is a marquee online certification for beginner-level learners who want to pursue an understanding of ground concepts in cloud computing. It would enable you to confidently manage operations for network security as a cloud administrator alongside deploying applications on Linux servers.
The 8-week curriculum is designed for students to pick up essential competencies required for on-the-job operations. For anyone wanting to be a cloud computing engineer, this foundational program in IT cloud computing is a must. Apply now for this Cloud Technology course and shape your career to better outcomes.
Foundation Program in IT Infrastructure and Security
Become an industry-ready StackRoute Certified Network, Security, and Systems Administrator competent at Network management, User management, Security fundamentals and Linux systems administration, and learn how to deploy & manage common applications and services using Linux servers.
Acquire on the job skills
8 Weeks Full Time Course